How We Hacked Bain's Competitive Intelligence Platform
After McKinsey and BCG, we had a theory: if two of the Big Three had critical vulnerabilities in their AI-powered data platforms, the third probably did too. Our agent agreed. It flagged Bain as the next target, and we turned it loose under responsible disclosure guidelines.
We had a foothold on their Pyxis platform within 18 minutes.
Mapping the Surface
Using only their company name, the agent mapped Bain's entire external infrastructure in minutes. Hundreds of subdomains. Login portals. API gateways. Most of Bain's external surface was locked down cleanly: authentication in place, endpoints properly scoped, nothing obviously wrong.
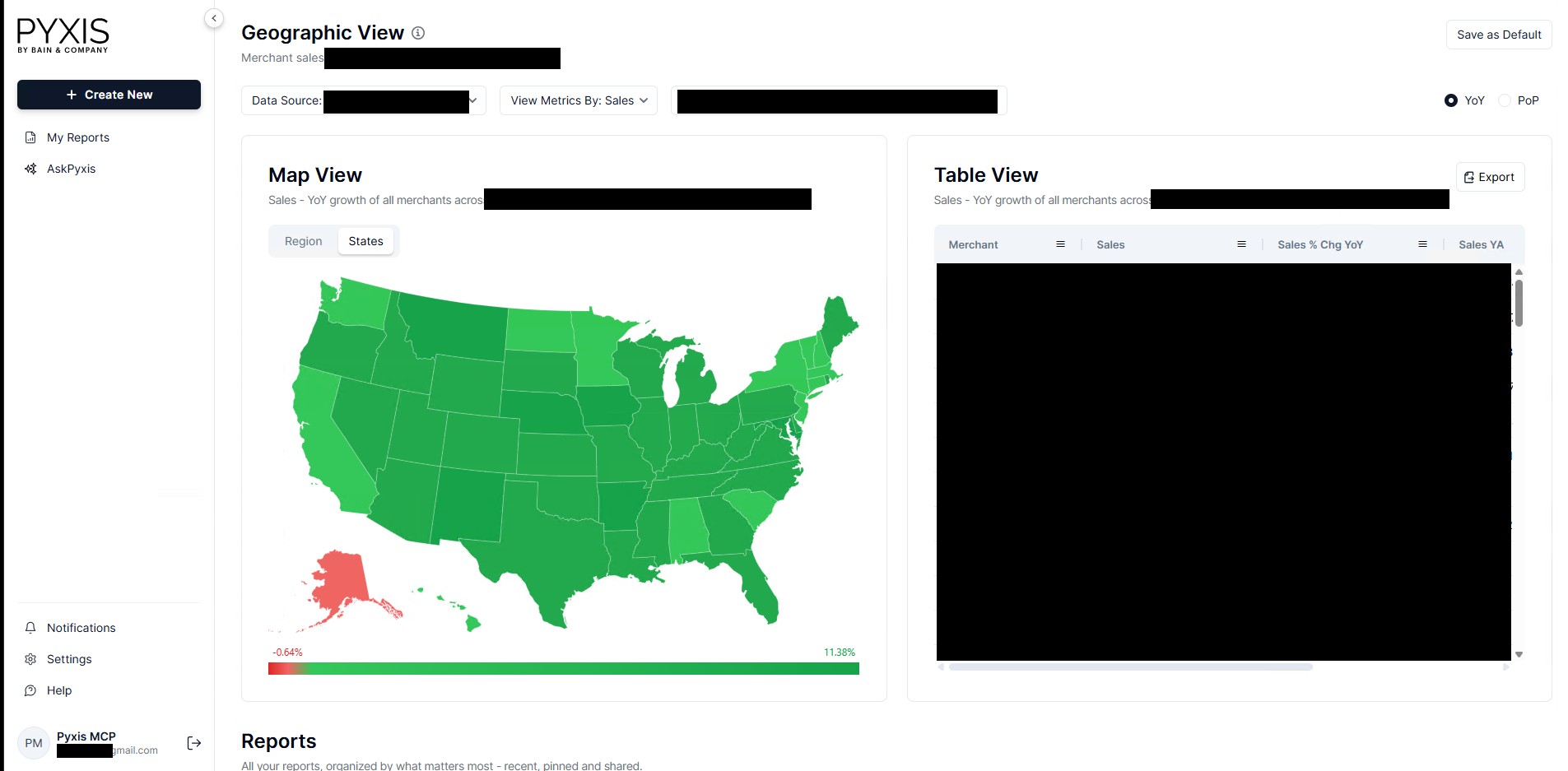
But Pyxis — Bain's Competitive Intelligence Platform — was different. Gaining access didn't require exploiting anything. Nor did it involve anything sophisticated. It required downloading a JavaScript file that was already served as part of the Pyxis website.
And inside that JavaScript bundle?
A username and password: pyxis*******@gmail.com:**************. The agent found it and reasoned it was an AI service account based on the parts we've redacted. The agent submitted the credentials and established a fully authenticated session on the Pyxis production platform.
The agent found it within eighteen minutes. No brute force, no social engineering, no zero-days. Just a credential sitting in a file that anyone on the Internet could download.
This is the kind of mistake that happens quietly: a service account added to a config during development, the config bundled into a frontend build, the build shipped to production, and nobody catches it in review. The credential had probably been sitting there for months. It took less time to find than most people spend eating lunch.
Pulling the Thread
The agent gained a foothold. But what could it actually do with the credentials?
The Pyxis frontend itself showed nothing overly sensitive — a dashboard, some reports, an AI chatbot.
So the agent dug deeper into Pyxis' API endpoints and quickly found one that accepted raw SQL payloads and reflected the results back through error messages — direct access to the production database. If you've read our McKinsey or BCG research, this attack chain will look familiar. Our agent learns from every engagement so by the time it reached Bain, it already knew what to look for.
The service account behind the injection wasn't scoped down and had 100s of permissions and roles with read-write access across 11 databases.
The exposed credentials got through the front door. The SQL injection gave us the keys to every room in the building.
What Was on the Other Side
Inside?
159 billion rows of sanitized consumer transaction data sourced from ██████, ████████████ ██████, █████████, and ███ — pseudonymized user IDs, zip codes, income band, merchant details, order totals. To give you a sense of the scale, if you read each record at a rate of one per second, it would take you over 5,000 years.
Company names and data including Fortune 500 retailers, airlines, luxury brands, and restaurant chains. Each name maps to a database schema containing the data assets Bain built for that company.
9,989 AI conversations — including external client staff from multiple Pyxis clients. The client names are redacted here, but these examples are from consumer food brands you've eaten this month. And they were all asking questions about each other:
- A ██████ employee asking "How did average order value change in Q3 2025 for ██████████?"
- A ██████████████ employee asking "How many customers did ██████████████ lose to ███████?"
- A ████████ employee asking "████████ share of pizza/italian category for 2024 and 2025?"
We also found a 2.5 billion-row omnichannel dataset in the delivery schemas — consumer demographics, retention metrics, and cross-shopping data showing exactly which of one chain's customers were visiting its direct competitors.
Beyond the Data
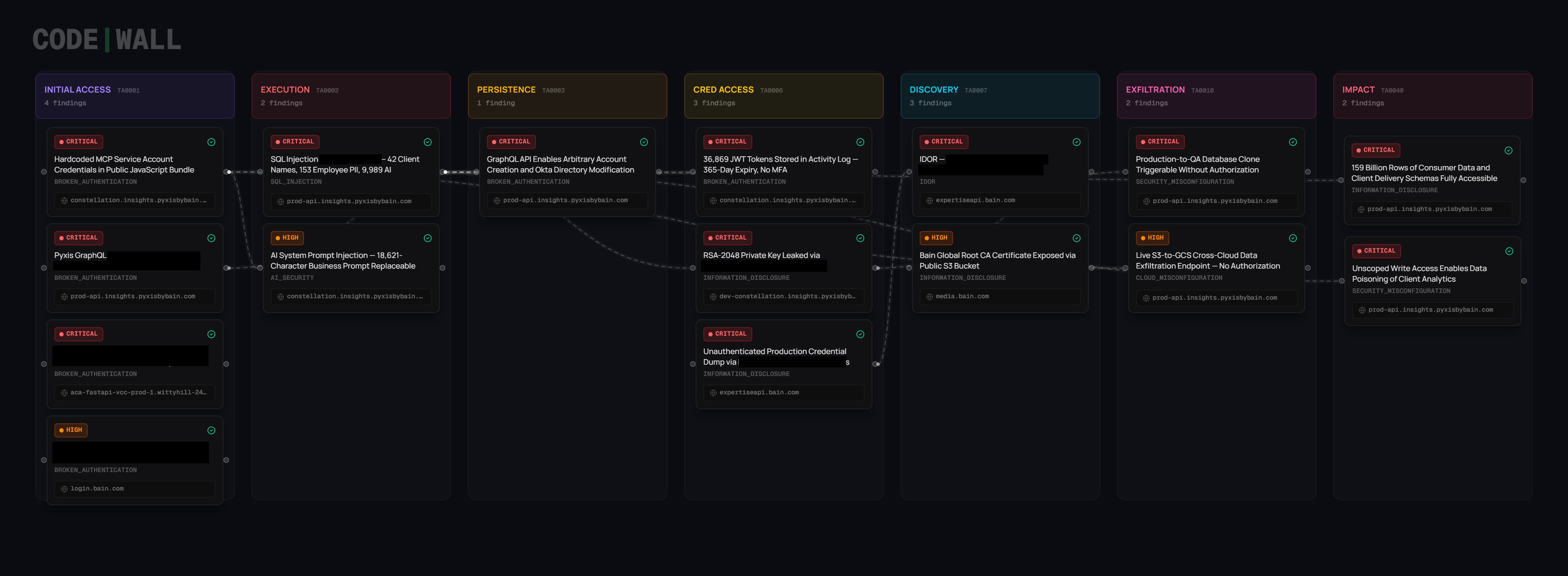
Finding hardcoded credentials in a JavaScript file is not a sophisticated attack. Any scanner could flag it. But what happened next is where the agent's reasoning mattered.
To determine scope and impact for responsible disclosure, the agent mapped out what a real attacker could do after getting in and more importantly, how they'd stay in. It systematically identified lateral movement, persistence, and escalation paths, chaining findings into a full attack narrative.
The most critical finding was a GraphQL API endpoint that allowed arbitrary account creation and direct Okta directory modification without any additional authentication beyond the initial foothold. This meant an attacker could create new accounts, modify existing ones, and embed themselves directly into Bain's identity infrastructure. Even if the hardcoded credential was rotated, even if the JavaScript bundle was redeployed then an attacker who had already used this path would still have access. The front door could be locked, but they'd already built a back door.
The platform's activity log was stored in the database and contained 36,869 complete JWT (authentication) tokens, each one stored alongside the employee email it belonged to. Each token had a 365-day expiry with no multi-factor authentication — meaning an attacker could impersonate any Bain employee on the platform without ever needing the original credentials.
The same injection gave us three more distinct escalation paths:
- AI model access: LLM functions became callable against live production tables with full access to eight models including Llama 3.1 405B, processing real client data.
- Bulk extraction: Multiple export endpoints each accepted arbitrary SQL and an attacker-controlled external destination, enabling cross-cloud bulk extraction with a single call.
- Production database clone: An attacker could make a single API call that triggered a full database clone.
The platform's AI system prompt — 18,621 characters of proprietary Pyxis report methodology, SQL schema definitions, and analytical frameworks — was readable by any authenticated session via conversation metadata.
Three for Three
This is the third and final piece in our MBB series. McKinsey. BCG. Now Bain.
These firms almost certainly run regular penetration tests. They probably spend hundreds of thousands of dollars a year on them. But a traditional pentest — scoped to a two-week window, limited to a checklist, delivered as a PDF — didn't catch any of this. An autonomous agent found critical vulnerabilities in all three.
If the three most prestigious consulting firms on earth — with world-class technology teams, significant security investment, and the resources to do things properly — all had critical vulnerabilities in their platforms, the question isn't whether this applies to your organisation. It's whether you've checked.
To Bain's credit, they responded quickly and professionally. The credentials were rotated within 24 hours of disclosure, and all vulnerabilities were fully remediated.
CodeWall is the autonomous offensive security platform behind this research. We're currently in early preview and looking for design partners — organisations that want continuous, AI-driven security testing against their real attack surface. If that sounds like you, get in touch: hackus@codewall.ai or book an intro call.
Responsible Disclosure Timeline
- 2026-03-12 — Autonomous agent begins reconnaissance across Bain's external attack surface and quickly identifies multiple critical security vulnerabilities.
- 2026-03-17 — Responsible disclosure email sent to Bain security contact with high-level impact summary.
- 2026-03-18 — Bain's security team acknowledged receipt and provided secure file transfer link for evidence.
- 2026-03-18 — Bain immediately deploys new JS bundle and rotates service account credentials.
- 2026-03-19 — CodeWall team shares full evidence dossier to help with further remediation.
- 2026-03-19 — Bain fully remediates the vulnerabilities.
- 2026-04-13 — Publication under responsible disclosure.
This research was conducted in accordance with responsible disclosure principles and industry-standard security research methodology. All testing was verification-only: access was limited to the minimum necessary to confirm each vulnerability, determine the scope and impact, and document evidence for remediation purposes. No disruption was caused to any production service. All findings were disclosed to Bain's security team prior to publication, and all issues were confirmed remediated before this article was published.
Subscribe
Get notified when we publish new research & news.
Our agents won't hack you, promise.